Hello Everyone
I hope you are all safe and healthy in this pandemic situation. I really miss my normal life and hope soon everything will be normal. However, today I will talk about one of the most used web application fuzzing tool WFuzz. But before we talk about this tool, let’s talk about fuzzing.
So, what is fuzzing ?
Fuzzing is a way of detecting bugs using automated processes that provide invalid, unexpected or random data as input to the application and then monitor the application’s behavior. The invalid data may be created for a specific purpose or may be generated randomly. The goal is to detect the unexpected behavior of an application and see if it leads to an exploitable bug.
Now, let’s talk about WFuzz tool.
WFuzz is created by Xavier Mendez aka Javi, Christian Martorella, Carlos del ojo and others. You can check out the Github repository for all contributors. This tool is designed with a general idea in mind that it replaces any reference to the FUZZ keyword by the value of the given payload. This simple concept allows any input injection in any case of an HTTP request, allowing the execution of complex web security attacks on various web application elements such as parameters, authentication, forms, directories / files, etc.
In one sentence the tool will simply replace the FUZZ keyword with your word or payload from the URL / request you provided.
Installation
WFuzz was created using the Python language. So you need to have Python installed to use it.
You can install WFuzz using PIP using the following command
pip install wfuzzYou can use the following commands to install the tool from the Debian (Kali, Parrot) repository
sudo apt update
sudo apt install wfuzz -yThis tool is available at Black Arch repositories. So if you are using an Arch Distribution with Black Arch repository, you can install it with the following command
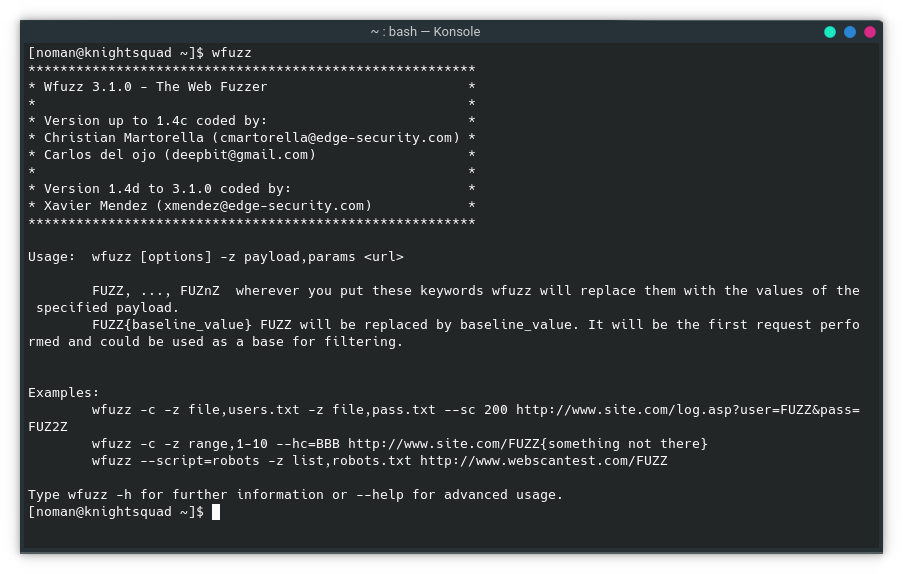
sudo pacman -Sy wfuzz --noconfirmThis tool is pre-installed in most of the penetration testing distributions like Black Arch. Run the following command on your terminal to verify the installation.
wfuzzAt the time of this writing, WFuzz command outputs the following:
Example Brute Force attack using WFuzz
Lets’ launch a simple brute force attack against a login form
wfuzz -z file, /home/noman/MrRobot/fsoc.dic --hs Invalid -d “log=elliot&pwd=FUZZ” http://192.168.0.129/wp-login.phpHere :
-z : payload/wordlist — the list you want to use for your brute force attack.--hs : ignore response containing given message/words-d : the post requestFUZZ : the section of the post data I want to fuzzConclusion
In this article I have tried to tell you about fuzzing and introduce you to WFuzz tool and also how you can install this tool in your Linux OS. I hope you enjoyed this article. And be sure to share your opinion in the comments section.
Happy Hacking 🙂


